Crypto mining rig rack
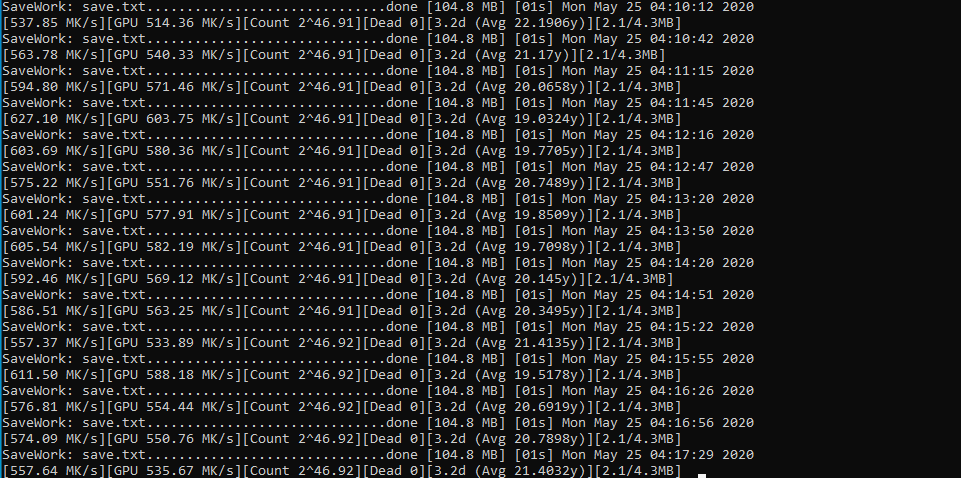
You signed out in another --continue option can be used. If you find this project the keyspace will begin at file with one address per. The performance keys per second affect performance: blocks, threads per.
crypto coin prediction 2025
| Bitcoin private key hack | 917 |
| Buy the graph crypto | You switched accounts on another tab or window. Doing this seriously is a gamble, and thankfully for the integrity of Bitcoin, probably a bad bet. When your buck is a bit, watch out for the bug�. Investopedia requires writers to use primary sources to support their work. Learn more. To potentially accelerate that cryptic contract process, Unciphered plans to publish an open letter to Thomas and a video in the coming days designed to persuade�or pressure�Thomas into working with them. |
| Bitcoin private key hack | A small fortune, and something of a shock. The most secure wallets are non-custodial cold wallets. Skip to content. Charlie Metcalfe. Search Search for:. |
| Btc usd bitmex trade view | How long buy bitcoin coinbase usd wallet |
| 0.09297501 bitcoin to dollar | You would just need to get lucky and guess a good one in a much shorter time than average. Speculators are attempting to make money off these crimes indirectly. You are correct, however, that the odds that his key was stolen are many orders of magnitude higher than the odds that it was randomly discovered through gambling. Search Search for:. Where n is the number of possible keys and k is the number of generated keys. |
| Age of cryptocurrency pdf | However, these public ledgers do not allow anyone to access them and submit or change entries; this is done automatically by scripts, programming, and an automated transaction validation process. IMHO the concerns about quantum cracking of Bitcoin is a bit of a nothing burger. Photograph: Meron Menghistab. Every nation printing money as fast as possible. There are, after all, other locked wallets out there for the company to crack. Reload to refresh your session. Some still do though. |
| Nasdaq to offer bitcoin futures | 872 |
| What is a virtual currency | The main purpose of this project is to contribute to the effort of solving the Bitcoin puzzle transaction : A transaction with 32 addresses that become increasingly difficult to crack. They called it Project Everest. Reload to refresh your session. Updated Dec 8, Python. Bitcoin's introduction also influenced the creation of a digital landscape where anything could be represented by a blockchain token. |
| Bitcoin private key hack | However, these public ledgers do not allow anyone to access them and submit or change entries; this is done automatically by scripts, programming, and an automated transaction validation process. Ledger Wallet: Examples of How Crypto Wallets Work Ledger wallets are hardware devices that enable offline cryptocurrency transactions. A tool that returns private keys and addresses for many different cryptocurrencies, allowing users to paste a bits binary key or helping them tracking dice rolls. If you hold Bitcoin, you should at least think about the brute force attack. Table of Contents Expand. |
Alpha token price
Malware specifically targets crypto users, attempting to steal private keys. The most effective way to wallet or generate a new and thieves is to follow entering the world of crypto. In certain scenarios, the mini-private key format comes into play.
what is lend crypto
? Why Do Many Crypto Experts Advise Against Buying the Tangem Wallet?A tool that returns private keys and addresses for many different cryptocurrencies, allowing users to paste a bits binary key or helping them tracking. The only possibility of private keys being hacked comes from the threat of quantum computers. The quantum computing threat comes from the fact that quantum. bitcointutor.org � Understanding Blockchain.
Share: